osint techniques
in the previous post (part 1) we have discussed about the reconniassance, its types and which type of data can be collected in the reconniasance. In this post we will discuss about that how can we collect that data by some techniques. and that is called manual osint techniques.
Disclammer: All the information about Reconnaissance given in this blog is for educational and ethical purposes only please don’t misuse it.
Read our terms and conditions for further information.
Read our privacy policy how data is collected.
First step in manual osint techniques
Before the hacking discussion can begin, first, one must protect one’s identity ethically and safely by creating an online persona. Here is how to proceed.
Fake Name Generator: There are websites like FakeNameGenerator that could be used to generate fake names and usernames. This further helps in establishing a false identity.

TempMail: Services like TempMail could be used to get temporary email addresses. Your actual email is not compromised, enabling you to register on social media. Keep in mind that these emails self-destruct shortly or when you close the website.
This Person Does Not Exist: Visit ThisPersonDoesNotExist.com to develop a fake profile picture of a nonexistent person.
Manual OSINT Techniques
Web browsers for osint techniques
Search for social media accounts of the target.
Check their posts, their followers, and who they are following for potential information.
Search their comments, events, and interactions for information about how they behave and with whom.

Website source code analysis osint techniques:
Look at the source code of a web page to uncover hidden links, directories, or developer comments.
Search for admin login pages or more sensitive information.
Public databases and archives:
Other than finding old versions of websites, compare them with current designs through the Wayback Machine (archive.org).
Investigate public registers for further information.

Reverse image search:
Use Google Reverse Image Search or similar tools to find specific persons or information relating to an image.
Such searching will work more effectively with reliable images and widely circulated pictures.
Google dorking:
Advanced searches could be used to find specific information on websites. For example, to search for PDF files on a specific site:
site:example.com filetype:pdf
This method helps narrow down search results to specific pages or file types.
Basic Syntax: use operators like site:, filetype:, and intitle: to narrow down your search results
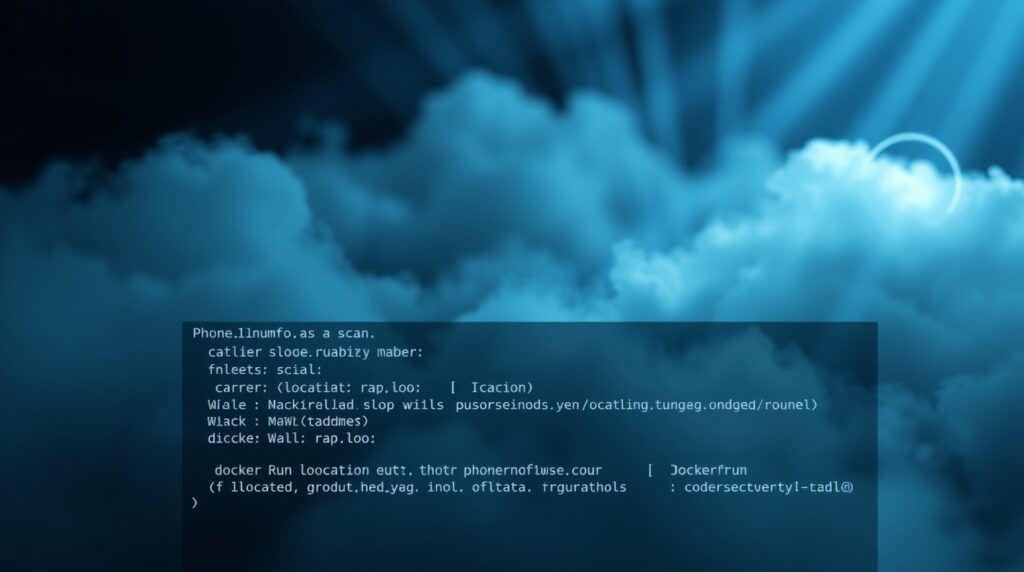
Phone investigation:
To gather information about a phone number you could use something like PhoneInfoga. The instructions on how to use it are below;
Installation of PhoneInfoga:
Make use of Docker to install and run PhoneInfoga in kali linux.
docker run --rm -it sundowndev/phoneinfoga:latest version.
This commands checks the version of PhoneInfoga.
Scanning of a particular number:
For scanning a specific number, type this command:
docker run –rm -it sundowndev/phoneinfoga scan -n
For example:
docker run --rm -it sundowndev/phoneinfoga scan -n 18004190157.
The command yields great results, providing details about carrier and location associated with the number.these commands are relatd to kali linux.
Gathering of information during the reconniassance is very helpful to perform penetration testing, but it is important to keep in mind that all the techniques should be used for ethical purposes only.
#osint, #ethicalhacking, #cybersecurity, #reconnaissance, #fakeidentity, #onlineprivacy, #socialmediaanalysis, #sourcecodeanalysis, #publicdatabases, #reverseimagesearch, #googledorking, #phonenumberinvestigation, #penetrationtesting, #informationgathering, #anonymity, #fakenamegenerator, #tempmail, #thispersondoesnotexist, #manualosint, #cybersecurityresearch, #digitalfootprint, #onlinesafety, #hackingtechniques, #cybersecuritytools, #dataprivacy, #ethicalhackingguide, #osinttechniques, #cybersecuritytips, #digitalinvestigation, #opensourceintelligence, #infosec, #cyberinvestigation, #hackers, #cyberawareness, #techsecurity, #digitalforensics, #cyberethics, #onlinetools, #cyberprotection, #hackingtools
if you want to perform ethical hacking and start free courses visit this link now
hackwithhusnain.com

Leave a Reply